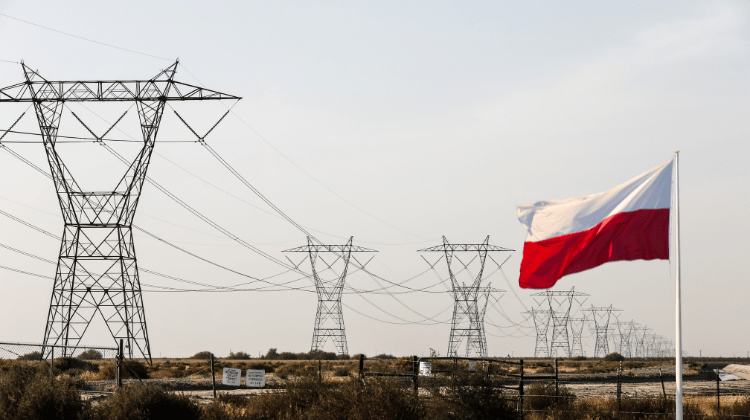
The next incident highlights the importance of visibility as a defense. In December 2025, Russian state-sponsored hackers from the Sandworm group launched a devastating cyberattack against Poland’s power grid, targeting combined heat and power plants and renewable energy management systems. Poland dodged a blackout. Officials called it the largest cyberattack the country had seen in years. It was stopped, but not by much. Ten years earlier, the same threat actor had successfully disrupted Ukraine’s power grid using the BlackEnergy malware. A decade on, critical infrastructure remains exposed. What exactly has failed to change, and why?
The answer lies in a persistent blind spot that continues to plague organizations worldwide: the failure to comprehensively map and monitor their attack surface.
The hidden attack surface problem
“The attack surface keeps expanding as cloud and remote work make it easy for teams to deploy new services without central oversight. Developers sometimes create their own environments to test or deploy applications, and these can sit outside security’s visibility,” notes Chris Boehm, field CTO at Zero Networks, in SecurityWeek’s Cyber Insights 2026 report on External Attack Surface Management.
This invisible expansion takes many forms:
- Shadow IT: departments adopting cloud services and SaaS applications without IT approval
- Forgotten Infrastructure: legacy systems, test environments, and development servers that remain exposed long after their purpose has ended
- Third-Party Connections: each supply chain partner and vendor integration creates potential pathways for attackers
- Misconfigured Services: default settings, open ports, and unpatched systems that slip through standard security processes
As Kevin Curran, IEEE senior member and professor of cybersecurity at Ulster University, explains: “By continuously finding and prioritizing internet-facing services, misconfigurations, expired certificates, dormant assets and third-party exposures, [organizations can] reduce the blind spots that lead to breaches.”
The core challenge is asymmetry: attackers need only find one weakness, while defenders must maintain perfect visibility across an ever-expanding digital footprint.
When the blast radius goes unmapped
The consequences of an incomplete attack surface picture become most apparent after initial compromise: when attackers begin lateral movement.
Consider the Poland power grid attack: Sandworm hackers deployed a new data-wiping malware, and had the attack succeeded, the blast radius would have extended from the initial entry point across interconnected operational technology (OT) systems, potentially cascading through multiple facilities before containment could begin.
This pattern repeats across sectors:
- Initial compromise through an overlooked entry point
- Reconnaissance to map internal systems and identify high-value targets
- Lateral movement through connected systems, privilege escalation, and data access
- Objective completion – whether data exfiltration, ransomware deployment, or destructive attacks
Organizations that lack visibility into their lateral movement paths discover the true scope of a breach only during incident response, when every hour counts. Without a pre-mapped blast radius, containment becomes a game of whack-a-mole rather than surgical isolation.
The cost of invisibility
According to IBM’s Cost of a Data Breach Report 2025, the global average cost of a data breach has reached $4 million USD. But the financial impact tells only part of the story:
Extended Dwell Time: attackers who exploit unmapped attack surface components often remain undetected for months. The longer they persist, the more data they exfiltrate and the more systems they compromise.
Compliance Failures: regulatory frameworks increasingly mandate comprehensive asset inventories and vulnerability management. Organizations that cannot document their attack surface face audit findings, fines, and remediation orders.
Incident Response Chaos: when breaches occur, teams without clear asset maps and an understanding of lateral movement scramble to answer fundamental questions: What systems are affected? What data was accessible? How far did the attacker get?
Brand and Trust Damage: no organization is too large or sophisticated to fall victim. The reputational impact compounds when breach disclosures reveal basic security gaps.
The path forward: continuous visibility
The evidence from recent incidents points to a clear imperative: organizations must achieve and maintain comprehensive visibility into their attack surface and potential blast radius.
This requires moving beyond point-in-time assessments toward continuous discovery and monitoring:
Complete Asset Discovery: every internet-facing system, forgotten subdomain, shadow IT deployment, and third-party integration must be identified and inventoried. Security cannot protect what it cannot see.
Blast Radius Mapping: understanding not just what’s exposed, but what happens if each entry point is compromised. Which systems can an attacker reach? What data becomes accessible? How far can the damage spread?
Prioritized Remediation: with complete visibility comes the ability to prioritize based on actual risk—focusing resources on the exposures most likely to be exploited and most damaging if compromised.
Continuous Monitoring: the attack surface is not static. New services are deployed, configurations change, and new vulnerabilities emerge. Visibility must be maintained through ongoing discovery and assessment.
Conclusion: visibility as the foundation
The incidents of recent weeks, from state-sponsored attacks on critical infrastructure to automated exploitation of exposed servers to social engineering campaigns against enterprise identity systems, share a common thread. In each case, attackers exploited gaps in organizational visibility.
The organizations that successfully defended against these threats, like Poland’s energy sector, preventing a power grid blackout, did so because they had sufficient awareness of their attack surface and response capabilities to contain the threat.
For security leaders evaluating their programs in 2026, the message is clear: prevention remains essential, but prevention without visibility is incomplete. Understanding what you have, what’s exposed, and what’s at risk if any component is compromised forms the foundation upon which all other security capabilities must be built.
The attack surface will continue to expand. The question is whether your visibility will expand as a result. This is why at Yonder, we developed an autonomous attack surface discovery service that will provide you with:
- Blast Radius Mapping: a visual representation of lateral movement paths, showing exactly what’s at risk from each entry point
- Asset Discovery: an inventory of all internet-facing or internal assets, including shadow IT, forgotten subdomains, and misconfigured services
- Risk Reduction Plan: actionable recommendations ranked by impact and effort
- Exposure Point Analysis: detailed breakdown of all entry points with risk levels and remediation guidance
References
- SecurityWeek, “Russian Sandworm Hackers Blamed for Cyberattack on Polish Power Grid,” January 2026
- SecurityWeek, “Cyber Insights 2026: External Attack Surface Management,” January 2026
By Alex Coman
Software Architect

Banner by Philipp Katzenberger, Unsplash
Book your free
1-hour consultation session
Yonder offers you a 1-hour free consultation with one of our experts. This is for software companies and enterprises and focuses on any concerns or queries you might have.
STAY TUNED
Subscribe to our newsletter today and get regular updates on customer cases, blog posts, best practices and events.